Overview
Bifrost can connect to any MCP-compatible server to discover and execute tools. Each connection is called an MCP Client in Bifrost terminology.Connection Types
Bifrost supports three connection protocols:| Type | Description | Best For |
|---|---|---|
| STDIO | Spawns a subprocess and communicates via stdin/stdout | Local tools, CLI utilities, scripts |
| HTTP | Sends requests to an HTTP endpoint | Remote APIs, microservices, cloud functions |
| SSE | Server-Sent Events for persistent connections | Real-time data, streaming tools |
Authentication is configured separately from the connection protocol. STDIO inherits its environment from the spawned subprocess and has no per-call auth. HTTP and SSE support five auth modes:
none, headers, oauth, per_user_oauth, per_user_headers. See Authentication →.STDIO Connections
STDIO connections launch external processes and communicate via standard input/output. Best for local tools and scripts.- Local filesystem operations
- Python/Node.js MCP servers
- CLI utilities and scripts
- Database tools with local credentials
HTTP Connections
HTTP connections communicate with MCP servers via HTTP requests. Ideal for remote APIs, microservices, and cloud-hosted MCP services.SSE Connections
Server-Sent Events (SSE) connections provide a persistent transport to MCP servers that stream events. Supports the same auth options as HTTP.- Real-time market data
- Live system monitoring
- Event-driven workflows
- Anything where the MCP server pushes notifications
Gateway Setup
- Web UI
- API
- config.json
Adding an MCP Client
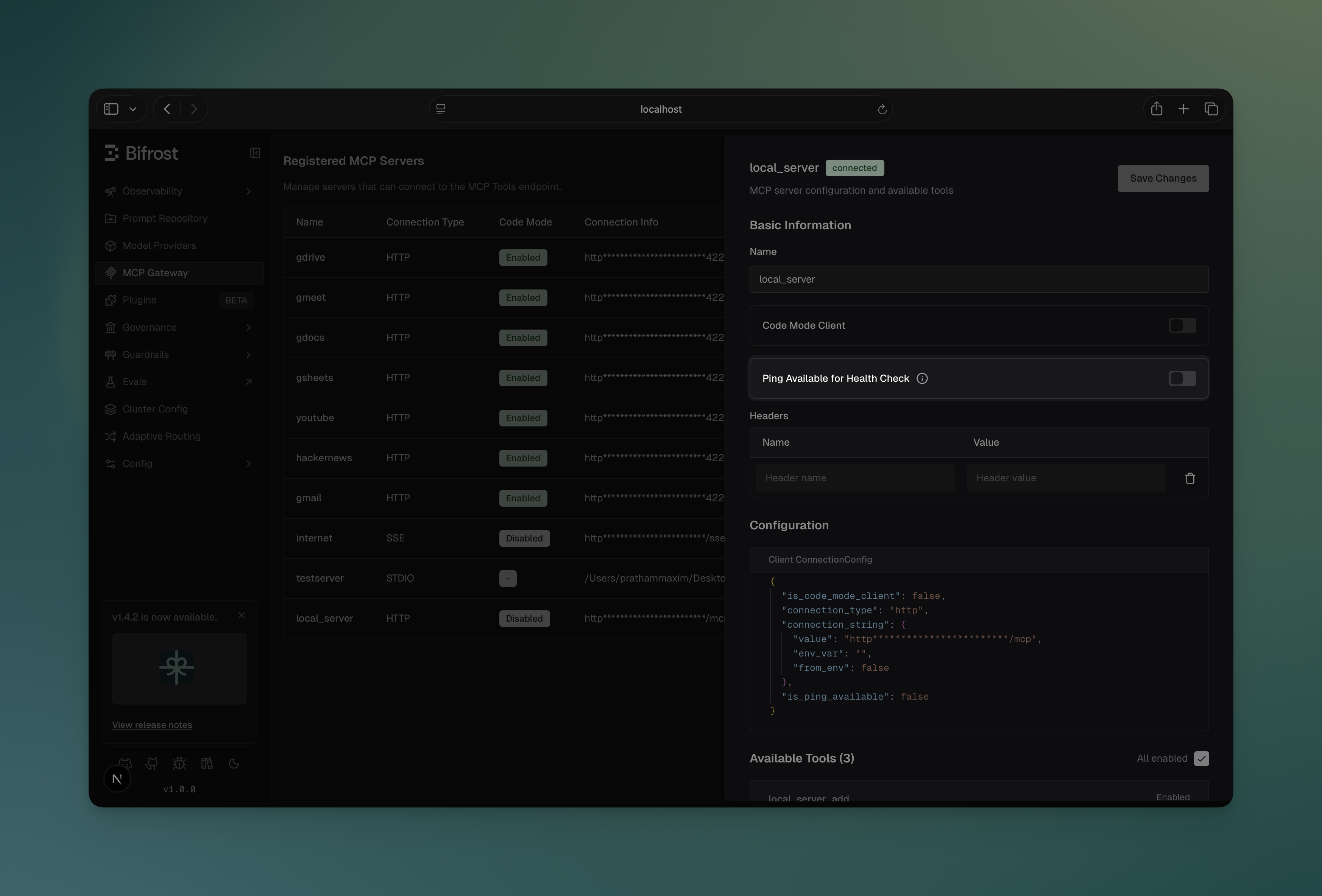
- Navigate to MCP Gateway in the sidebar - you’ll see a table of all registered servers
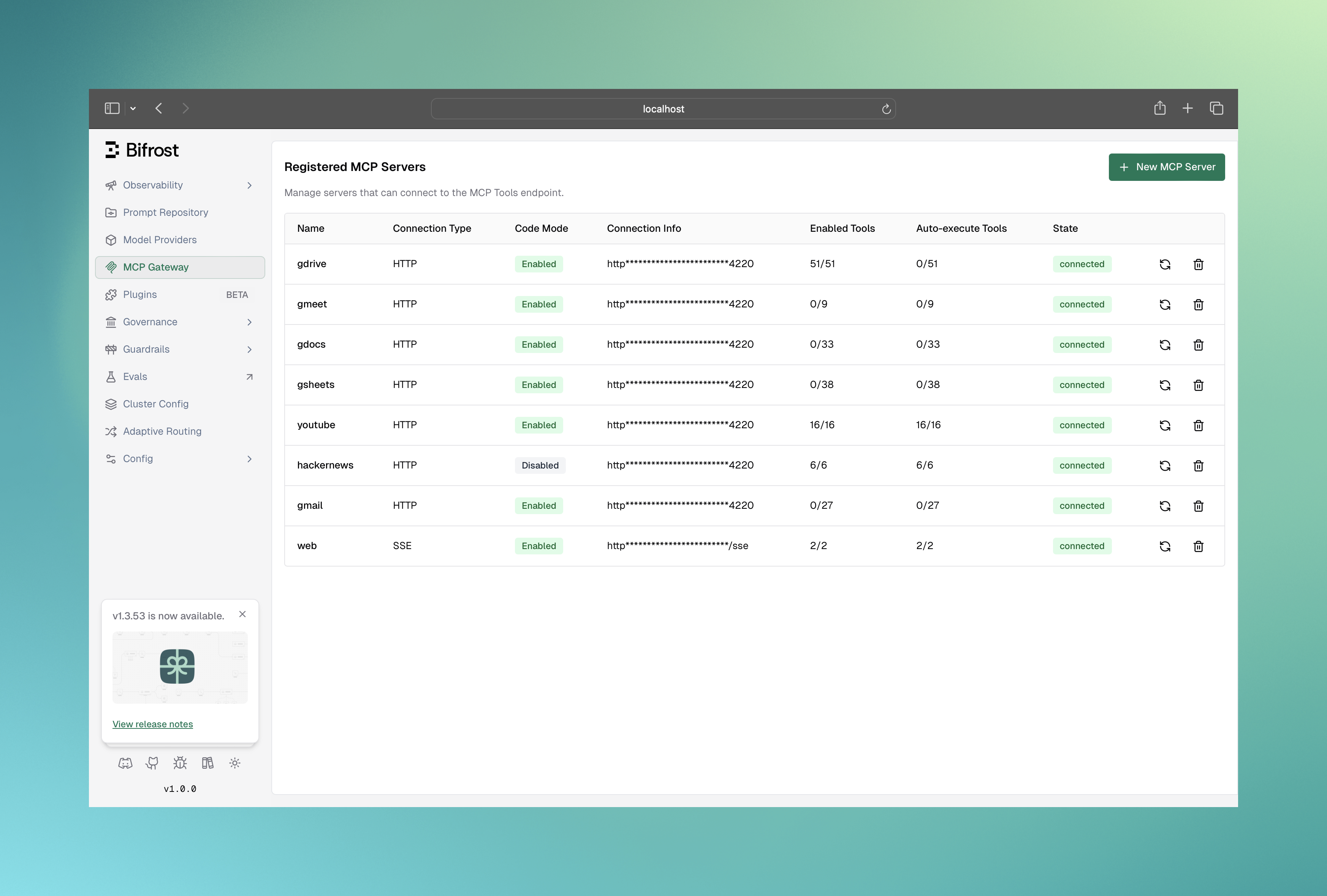
- Click New MCP Server button to open the creation form
- Fill in the connection details:
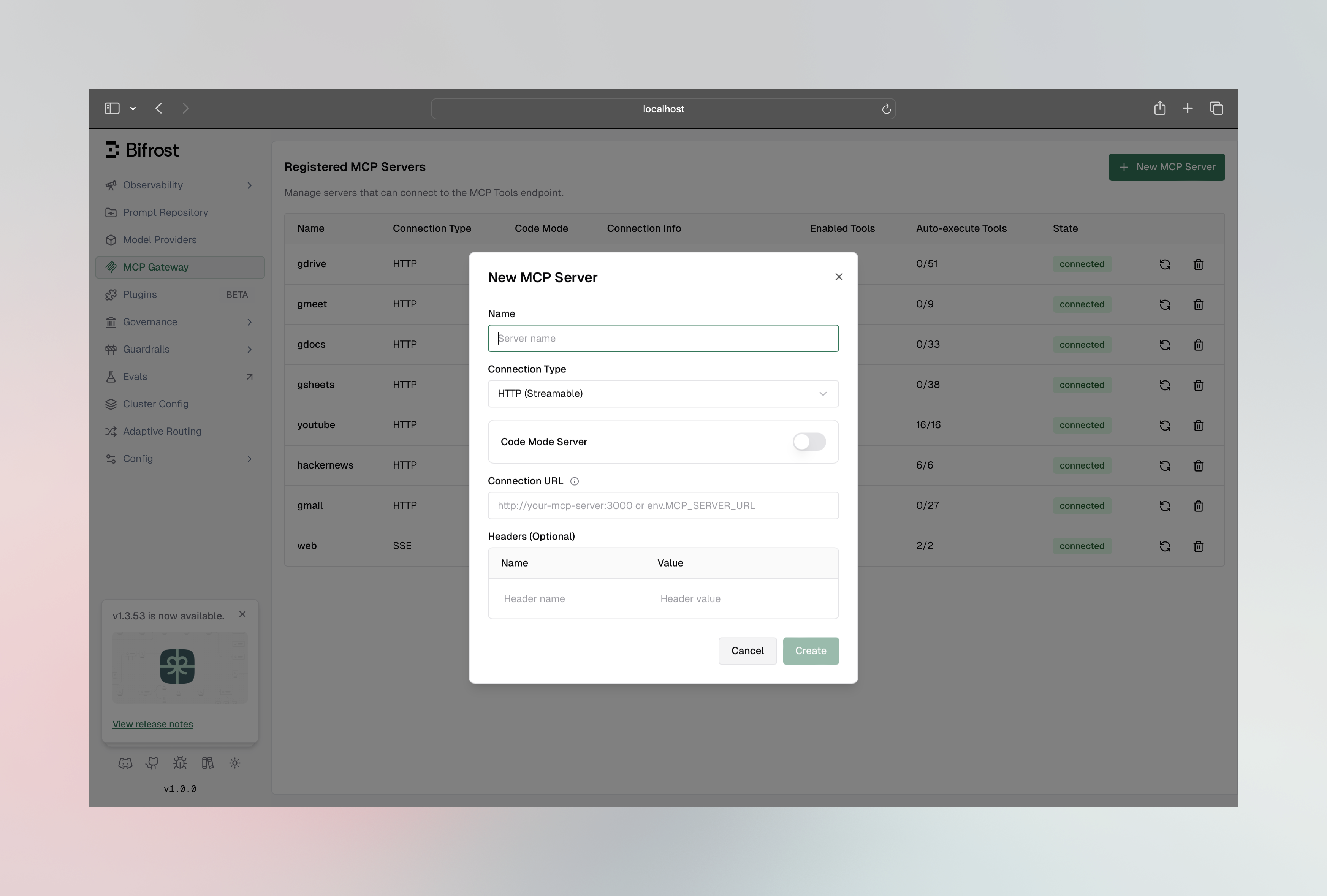
- Name: Unique identifier (no spaces or hyphens, ASCII only)
- Connection Type: STDIO, HTTP, or SSE
- For STDIO: Command, arguments, and environment variables
- For HTTP/SSE: Connection URL
- Click Create to connect
Viewing and Managing Connected Tools
Once connected, click on any client row to open the configuration sheet: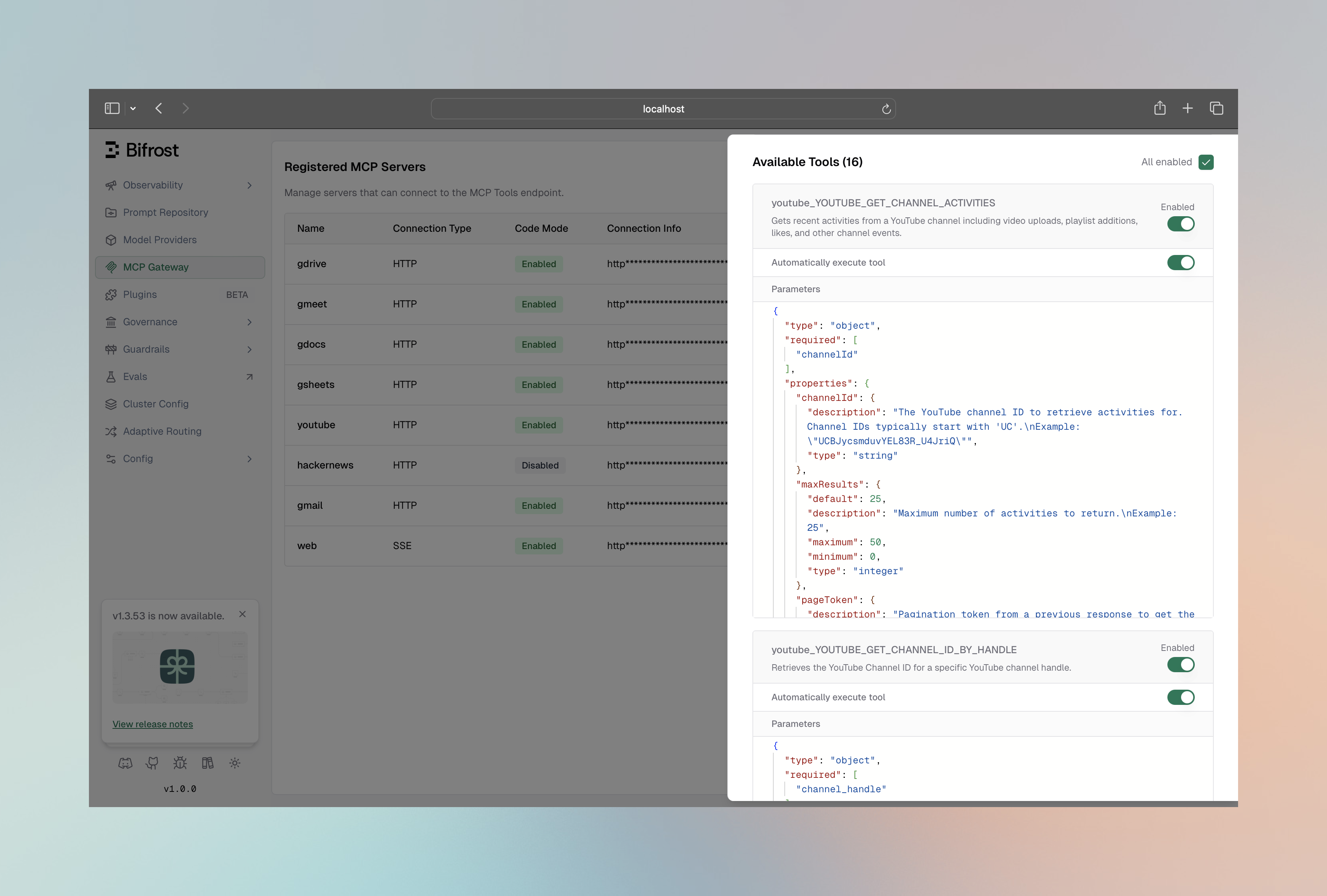
- View all discovered tools with their descriptions and parameters
- Enable/disable individual tools via toggle switches
- Configure auto-execution for specific tools
- Edit custom headers for HTTP/SSE connections
- View the full connection configuration as JSON
Go SDK Setup
Configure MCP in your Bifrost initialization:Tools To Execute Semantics
TheToolsToExecute field controls which tools from the client are available:
| Value | Behavior |
|---|---|
["*"] | All tools from this client are included |
[] or nil | No tools included (deny-by-default) |
["tool1", "tool2"] | Only specified tools are included |
Tools To Auto Execute (Agent Mode)
TheToolsToAutoExecute field controls which tools can be automatically executed in Agent Mode:
| Value | Behavior |
|---|---|
["*"] | All tools are auto-executed |
[] or nil | No tools are auto-executed (manual approval required) |
["tool1", "tool2"] | Only specified tools are auto-executed |
A tool must be in both
ToolsToExecute and ToolsToAutoExecute to be auto-executed. If a tool is in ToolsToAutoExecute but not in ToolsToExecute, it will be skipped.Global Tool Manager Settings
Tool-manager behaviour is configured once and applies to every MCP server. There are no per-server overrides for these four knobs — the only per-server tool-manager-adjacent setting istool_sync_interval on each client_configs[] entry.
| Field | Type | Default | Description |
|---|---|---|---|
tool_execution_timeout | integer / string | 30 | Tool-call upstream timeout. Integer = seconds, string = Go duration (e.g. "2m"). |
max_agent_depth | integer | 10 | Maximum recursion depth in agent mode. |
code_mode_binding_level | string | — | "server" or "tool" — controls how tools are exposed in the code-mode VFS. |
disable_auto_tool_inject | boolean | false | When true, MCP tools are not auto-injected into requests; callers must opt in via x-bf-mcp-include-tools (for LLM calls) |
- Web UI
- API
- config.json
- Go SDK
The MCP configuration panel under Settings → MCP exposes these four knobs plus 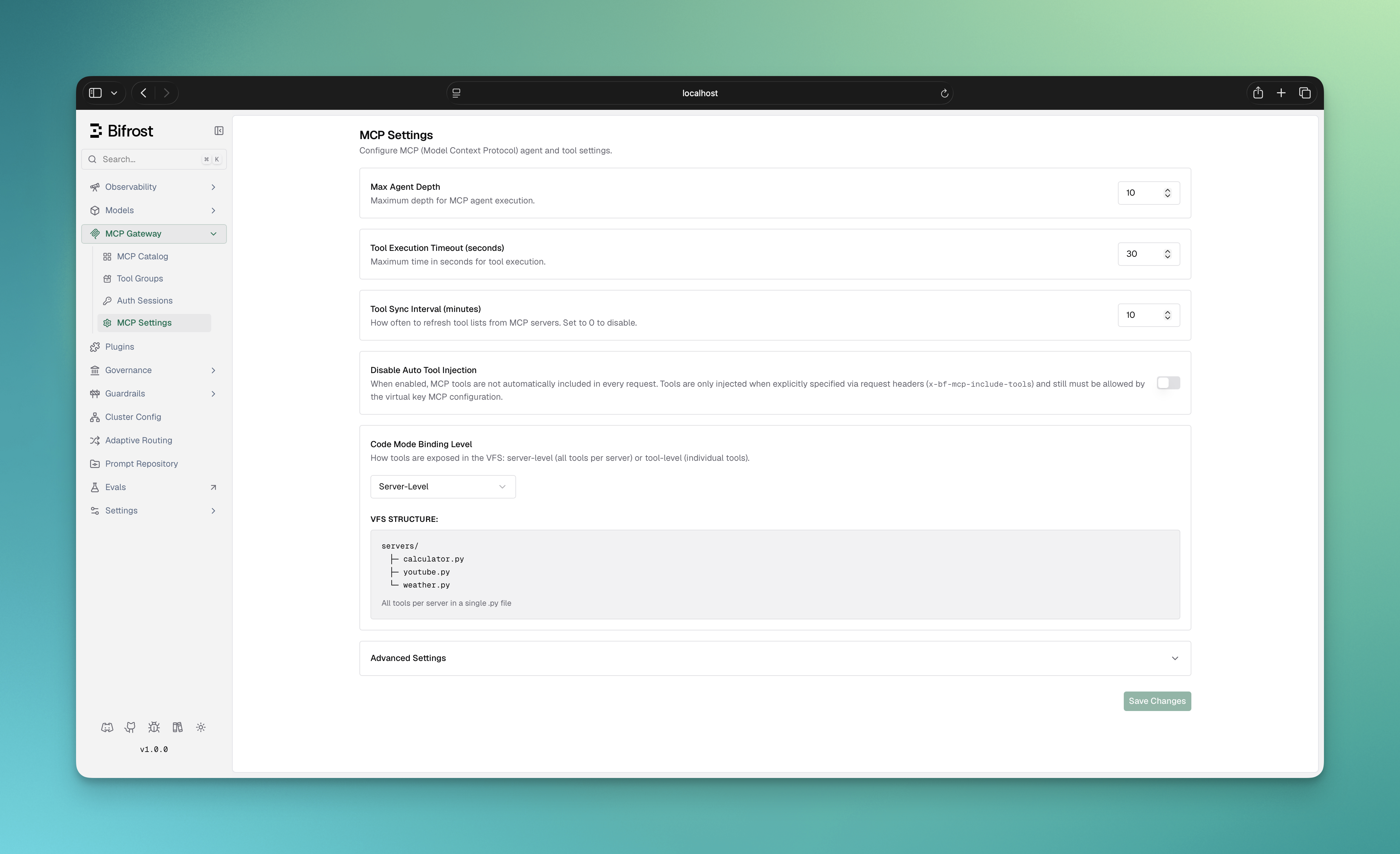
tool_sync_interval: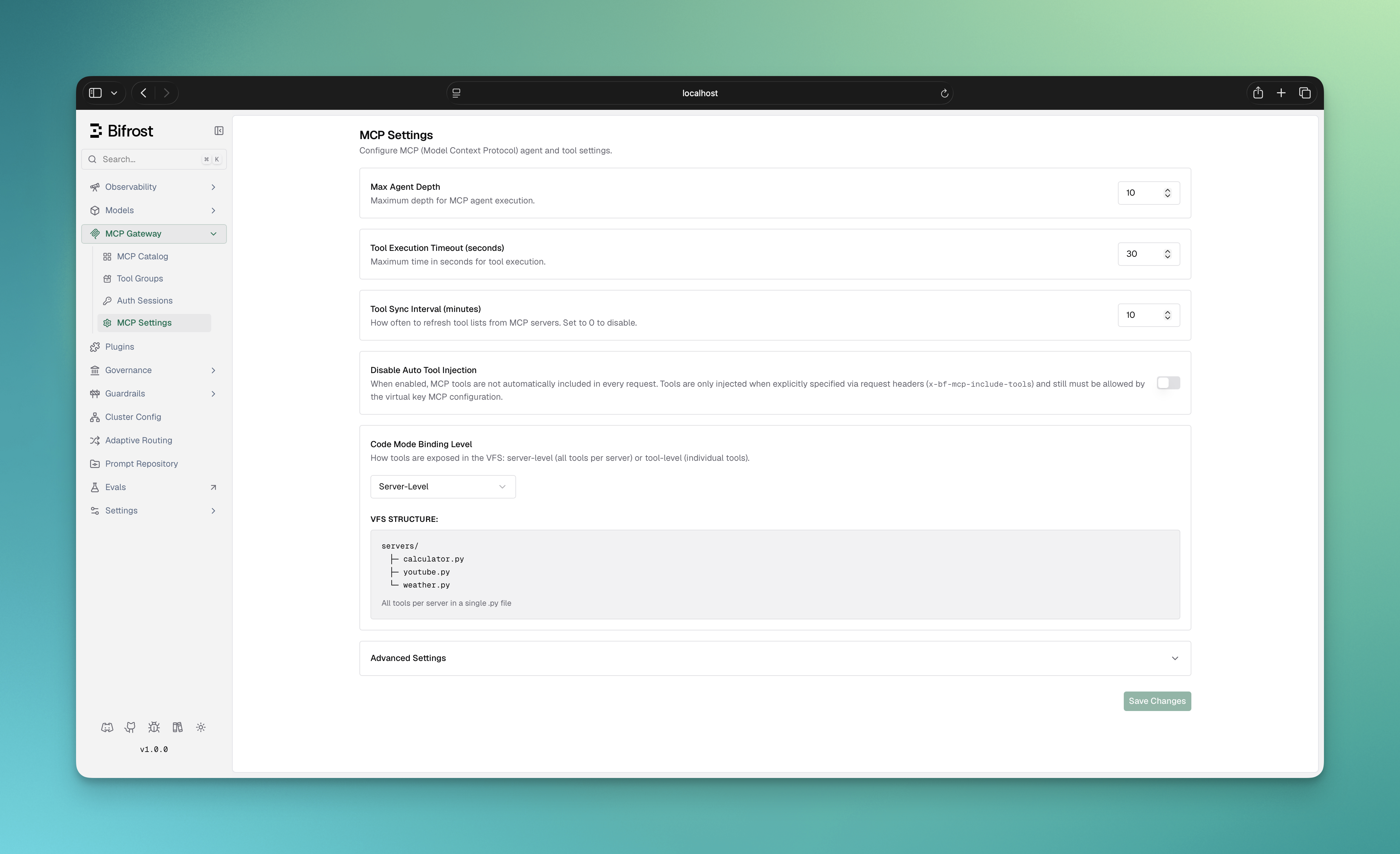
client.mcp_tool_execution_timeout, client.mcp_agent_depth, client.mcp_code_mode_binding_level, and client.mcp_disable_auto_tool_inject fields are deprecated aliases kept for backward compatibility — prefer mcp.tool_manager_config.* in new config.json and Go SDK setups. The Web UI panel and /api/config continue to use the aliases because they edit the live client_config row directly.
Environment Variables
Use environment variables for sensitive configuration values: Gateway (config.json):- Automatically resolved during client connection
- Redacted in API responses and UI for security
- Validated at startup to ensure all required variables are set
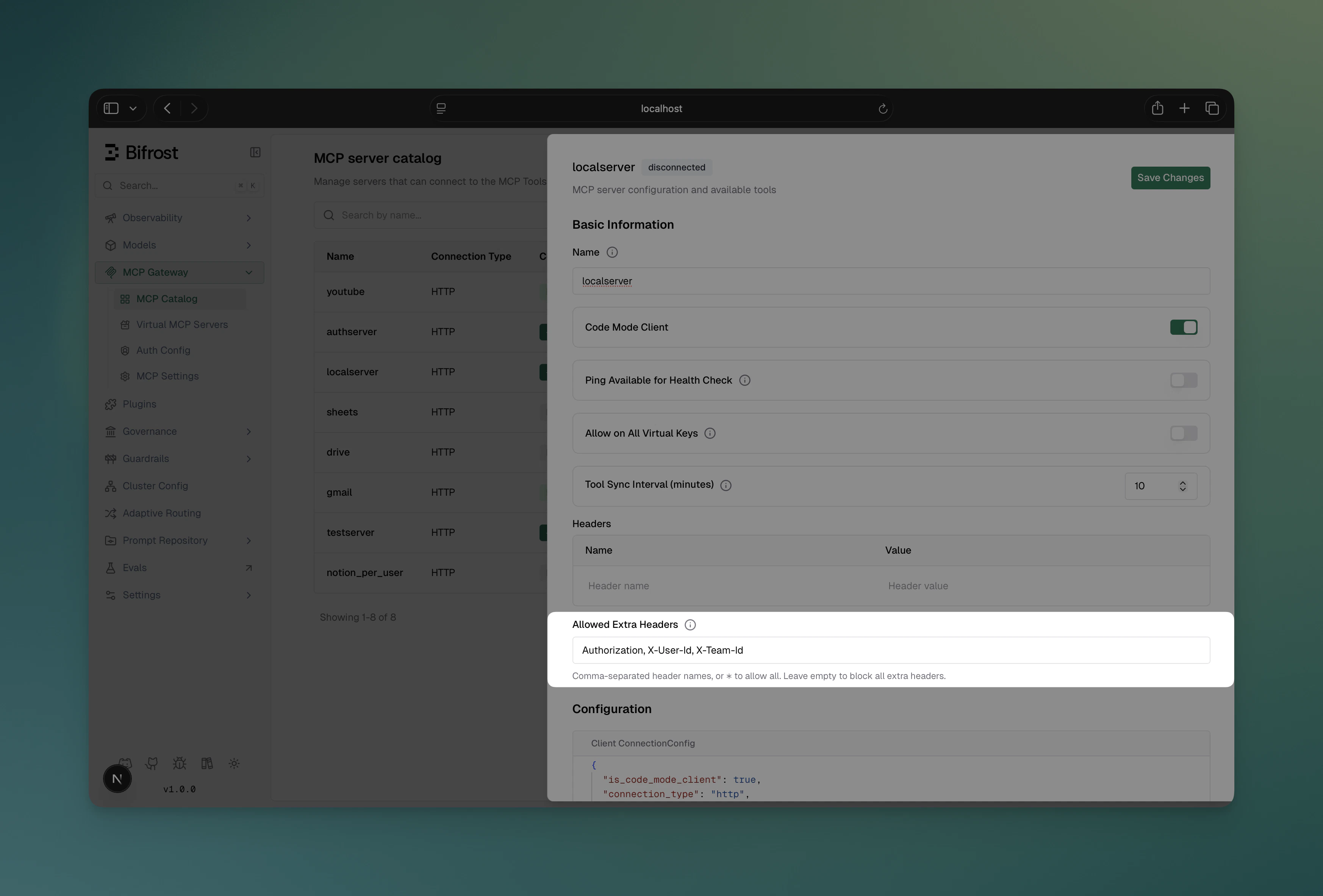
Forwarding Request Headers to MCP Servers
Header Forwarding is available in v1.5.0-prerelease1 and above.
allowed_extra_headers field lets you define a per-client allowlist of headers that callers may inject at request time and have forwarded to that MCP server when tools are executed.
This is separate from the static headers field used for authentication:
| Field | Purpose | When sent |
|---|---|---|
headers | Static auth credentials (API keys, tokens) | Always, on every tool call |
allowed_extra_headers | Dynamic per-request headers from callers | Only when the caller provides them, and only if they match the allowlist |
- Forwarding a user’s auth token to an MCP server that enforces per-user authorization
- Passing a tenant or org ID to a multi-tenant MCP server
- Propagating trace or correlation IDs for end-to-end observability
How It Works
- An incoming request carries one or more headers matching a client’s
allowed_extra_headerspattern - Bifrost captures those headers from the request (using the union of all clients’ allowlists)
- At tool execution time, each client re-checks the header against its own allowlist - so the same header can be forwarded to one MCP server but not another
Headers are matched case-insensitively. The only wildcard supported is a standalone
"*" (allow all headers) - partial patterns like x-tenant-* are not supported. If "*" is used, it must be the only entry in the list.- UI
- Management API
- Config File
- MCP Gateway (/mcp)
- Go SDK
Configure: Navigate to MCP Gateway, open the configuration sheet for an HTTP or SSE client, and set the Allowed Extra Headers field: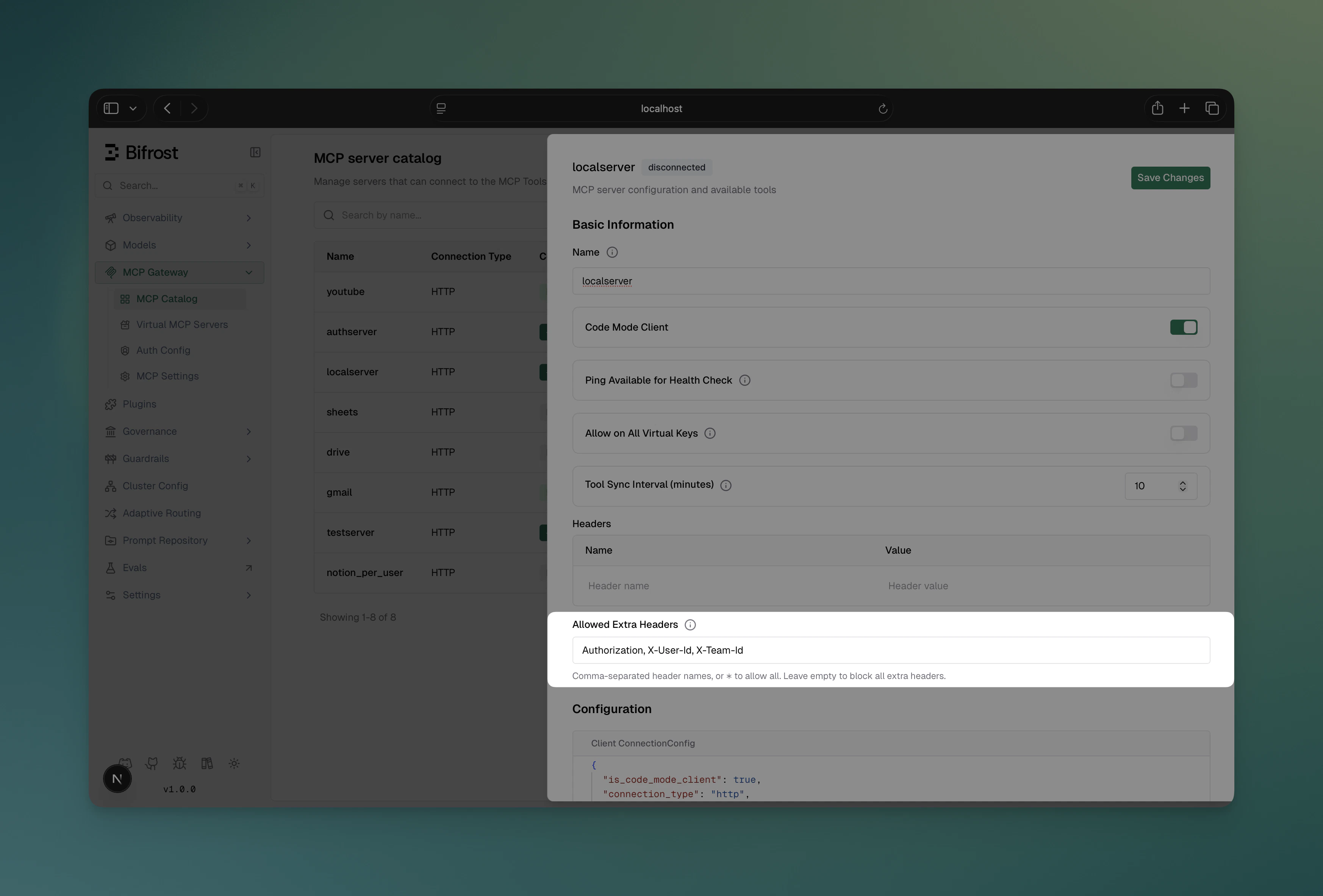
Client State Management
Connection States
| State | Description |
|---|---|
connected | Client is active and tools are available |
connecting | Client is establishing connection |
disconnected | Client lost connection but can be reconnected |
error | Client configuration or connection failed |
Managing Clients at Runtime
- Gateway API
- Go SDK
Reconnect a client:Edit client configuration:Remove a client:
Health Monitoring
Bifrost automatically monitors MCP client health with periodic checks every 10 seconds by default.Health Check Methods
By default, Bifrost uses the lightweight ping method for health checks. However, you can configure the health check method based on your MCP server’s capabilities:| Method | When to Use | Overhead | Fallback |
|---|---|---|---|
| Ping (default) | Server supports MCP ping protocol | Minimal | Best for most servers |
| ListTools | Server doesn’t support ping, or you need heavier checks | Higher | More resource-intensive |
Configuring Health Check Method
You can toggle theis_ping_available setting for each client:
Via Web UI
- Navigate to MCP Gateway and select a server
- In the configuration panel, toggle “Ping Available for Health Check”
- Enable: Uses lightweight ping for health checks
- Disable: Uses listTools method for health checks instead
Via API
Via config.json
Via Go SDK
Health Check Behavior
When a client disconnects:- State changes to
disconnected - Tools from that client become unavailable
- You can reconnect via API or UI
is_ping_available takes effect immediately without requiring a client reconnection.
Connection Resilience and Retry Logic
Bifrost automatically implements exponential backoff retry logic to handle transient network failures and temporary service unavailability. This ensures that brief connection issues don’t immediately cause tool unavailability.Automatic Retry Strategy
Bifrost retries failed operations using the following strategy, as implemented byExecuteWithRetry and DefaultRetryConfig in the MCP layer:
| Parameter | Value | Description |
|---|---|---|
Max Retries (DefaultRetryConfig.MaxRetries) | 5 | Retries after the initial attempt (6 attempts total) |
Initial Backoff (DefaultRetryConfig.InitialBackoff) | 1 second | Starting backoff duration before doubling |
Max Backoff (DefaultRetryConfig.MaxBackoff) | 30 seconds | Maximum wait time between retries |
| Backoff Multiplier | 2x | Exponential growth between attempts |
ExecuteWithRetry with DefaultRetryConfig):
- Attempt 1: Initial attempt (no wait)
- Attempt 2: Wait 1s, then retry (and double backoff to 2s)
- Attempt 3: Wait 2s, then retry (and double backoff to 4s)
- Attempt 4: Wait 4s, then retry (and double backoff to 8s)
- Attempt 5: Wait 8s, then retry (and double backoff to 16s)
- Attempt 6: Wait 16s, then retry (backoff capped at 30s max)
Error Classification
Bifrost intelligently classifies errors as either transient (retryable) or permanent (fail immediately): Transient Errors (Retried):- Connection timeouts or refused connections
- Network unreachable errors
- DNS resolution failures
- HTTP 5xx errors (500, 502, 503, 504)
- HTTP 429 (Too Many Requests)
- I/O errors and broken pipes
- Temporary service unavailability
- Context deadline exceeded or cancelled - Retrying won’t help if time limit is reached
- Authentication failures (401, 403)
- Authorization denied
- Configuration errors (invalid auth, invalid config)
- File or command not found (e.g., “command not found: npx”)
- Bad request errors (400, 405, 422)
- Command execution permission denied
- Invalid credentials
What Operations Are Retried
Bifrost applies retry logic to these critical operations:- Connection Creation - Establishing initial connection to the MCP server (with error classification)
- Transport Start - Starting the transport layer (STDIO, HTTP, SSE)
- Client Initialization - Initializing the MCP client protocol
- Tool Discovery - Retrieving available tools from the server
- Automatic Reconnection - When health checks detect disconnection
Reconnection on Health Check Failure
When a client reaches 5 consecutive health check failures:- Client state changes to
disconnected - Bifrost automatically attempts reconnection in the background
- Reconnection uses the same exponential backoff retry logic
- Once reconnected, health checks resume normal operation
- Tools become available again without manual intervention
Manual Reconnection
You can also trigger manual reconnection at any time:- Gateway API
- Go SDK
Benefits
- Handles transient failures: Brief network hiccups won’t cause tool unavailability
- Prevents server overload: Exponential backoff prevents hammering servers
- Automatic recovery: Disconnected clients reconnect automatically
- Production-ready: No manual intervention needed for temporary issues
- Transparent logging: Detailed retry attempts logged for debugging
Disabling and Re-enabling Clients
You can temporarily disable an MCP client without removing it. When disabled, Bifrost shuts down the client’s connection, health monitor, and tool syncer. The client entry is preserved and its tools are invisible to inference requests until it is re-enabled.- Web UI
- Gateway API
- config.json
Use the Enabled toggle in the MCP Server Catalog table to disable or re-enable a client with a single click. The toggle shows a loading spinner while the API call is in flight and automatically reflects the updated state.

disabled state persists across restarts — a disabled client is loaded into memory on boot but its connection is not established until it is explicitly re-enabled. Config changes (name, tools, headers) sent in the same PUT request as a disabled change are applied before the connection is shut down or re-established.
Naming Conventions
MCP client names have specific requirements: Valid names:filesystem, web_search, myAPI, tool123
Invalid names: my-tools, web search, 123tools, datos-api
Next Steps
Tool Execution
Learn how to execute tools from connected MCP servers
Agent Mode
Enable autonomous tool execution with auto-approval

